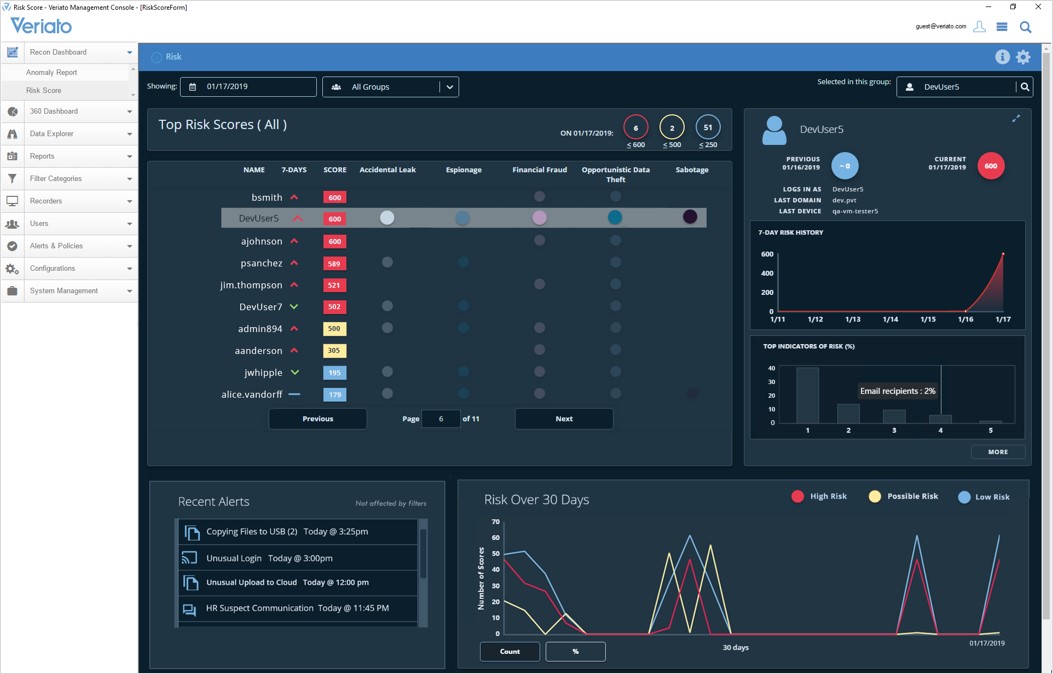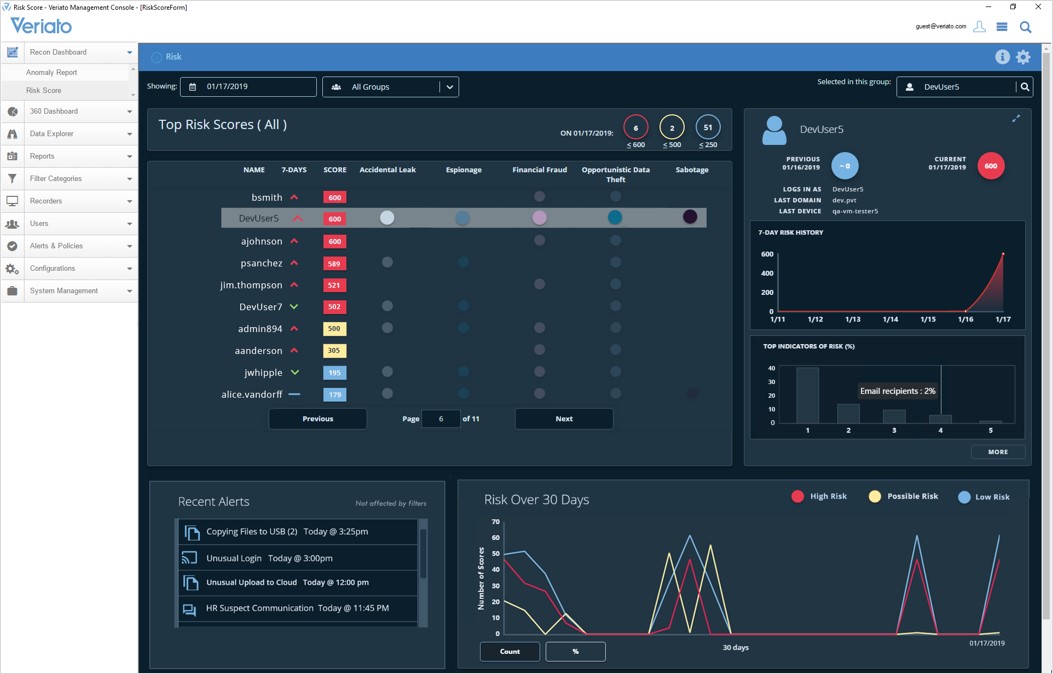
Risk scores – Veriato Management console
Veriato Cerebral, (aka Veriato 360) is one of the very early companies in the computer monitoring industry, the first version of the product was released in 1998. A huge number of companies around the world use these tools for tracking their employees.
A pretty powerful software for keeping tabs on almost every aspect of computer usage, whose developers boast an extensive toolset helping managers to stay in the loop on what their staff is doing.
Veriato, despite being one of the thought-through solutions on the market, is pretty comprehensive as well, and it might take a while to get the hang of it.
Fees
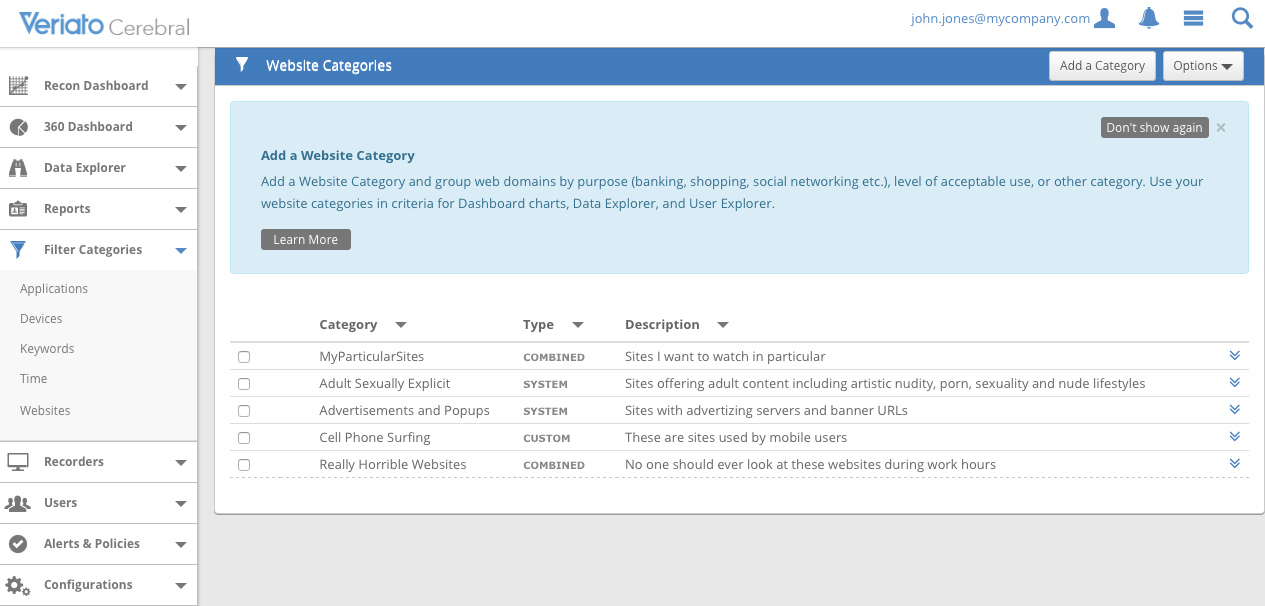
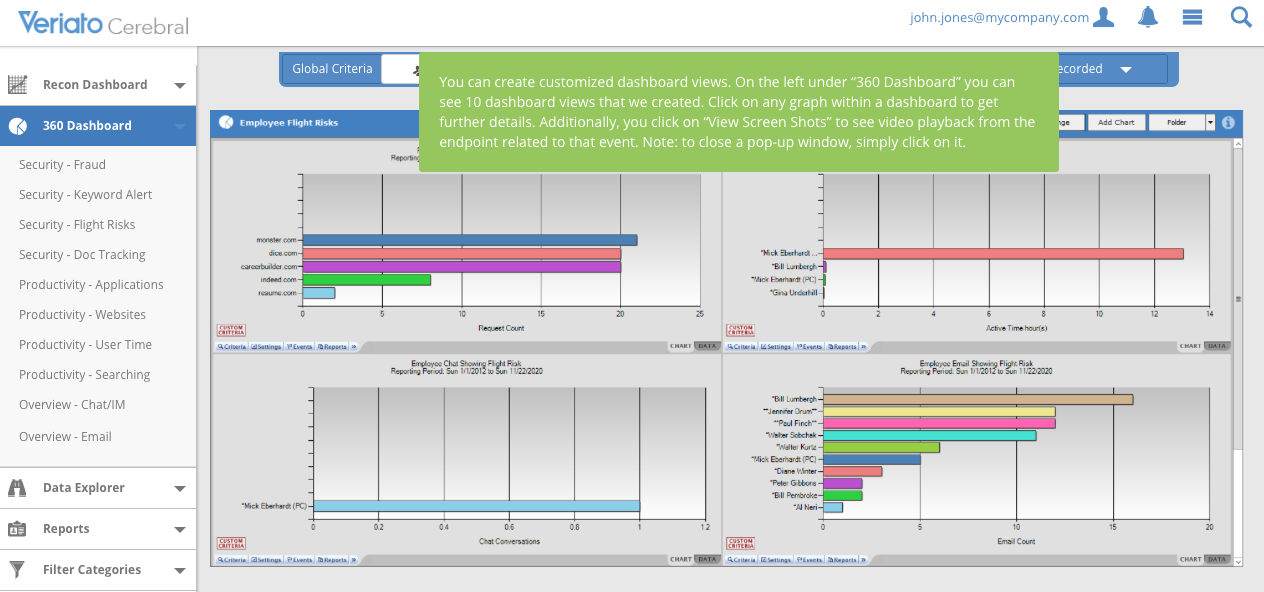
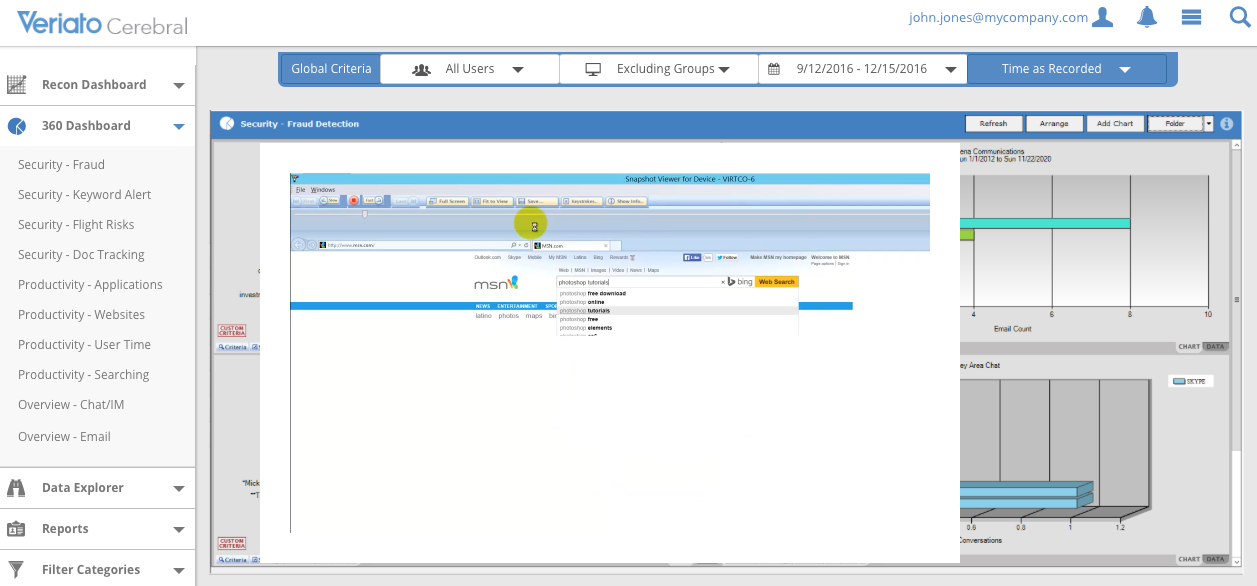
The overview of the interface
In this respect Veriato Cerebral is not like the other products – its owners don’t charge a fixed fee. Clients have to submit their contact details to get an estimate price from the Veriato sales team.
There was a request sent to the team of 10 employees for a test. Veriato representatives replied quickly, on the same day, saying it would cost $1,200 a year to monitor 10 users, which translates to $10 per user/month. Thus, the start-up fee is $95 per person a year. In the way, the more employees you’ve got, the less average cost you’ll have.
Veriato primarily targets companies with more than 50 users, but currently, the developers of the software are working on another version for smaller teams.
So, it’s not the most high-priced product around – with a standard cost per seat about $7.92 a month.
Features
It’s a full-fledged solution for monitoring that consists of a set of tools, including some advanced features that will tell you about all the nuts and bolts of the workforce’s actions, their behavior, and device usage.
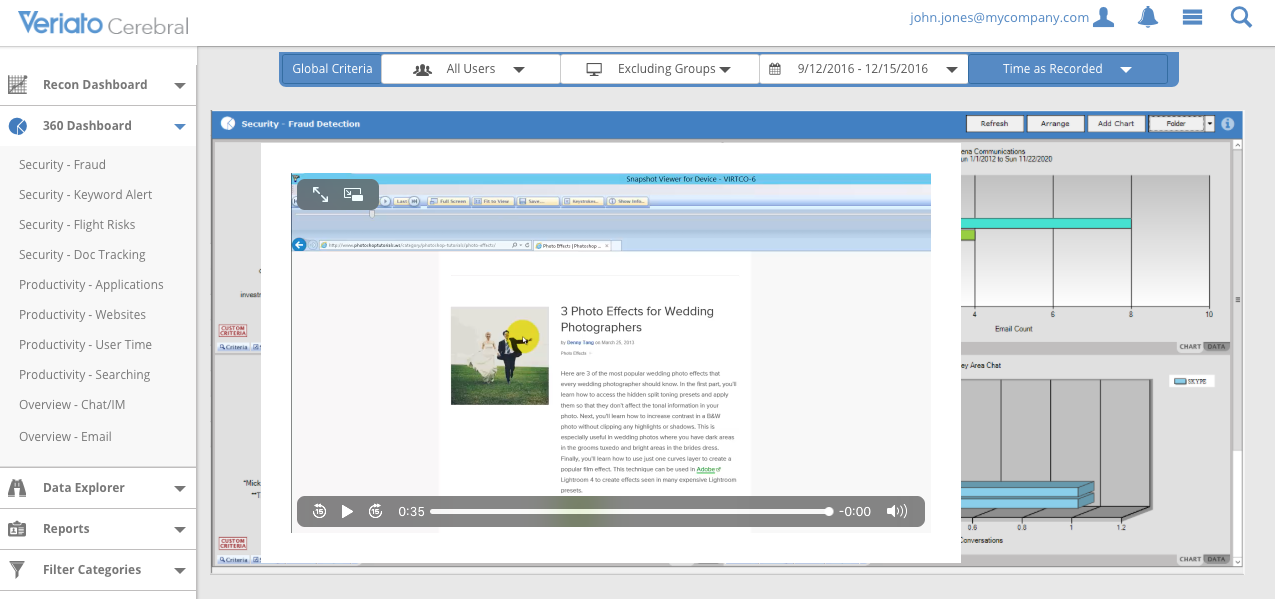
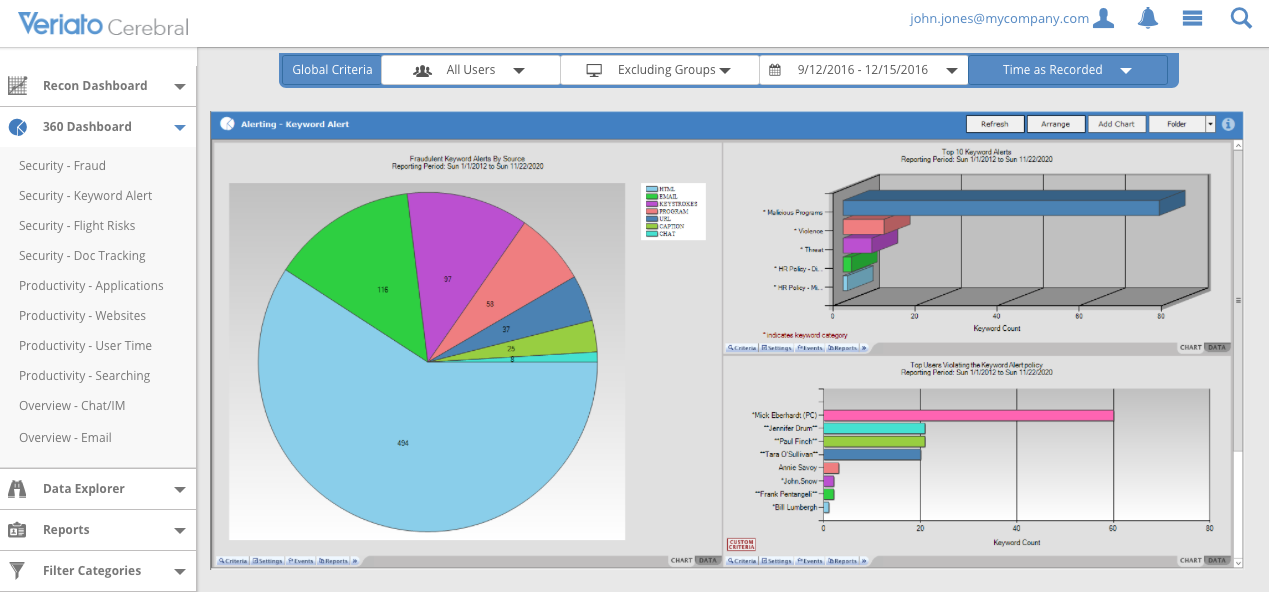
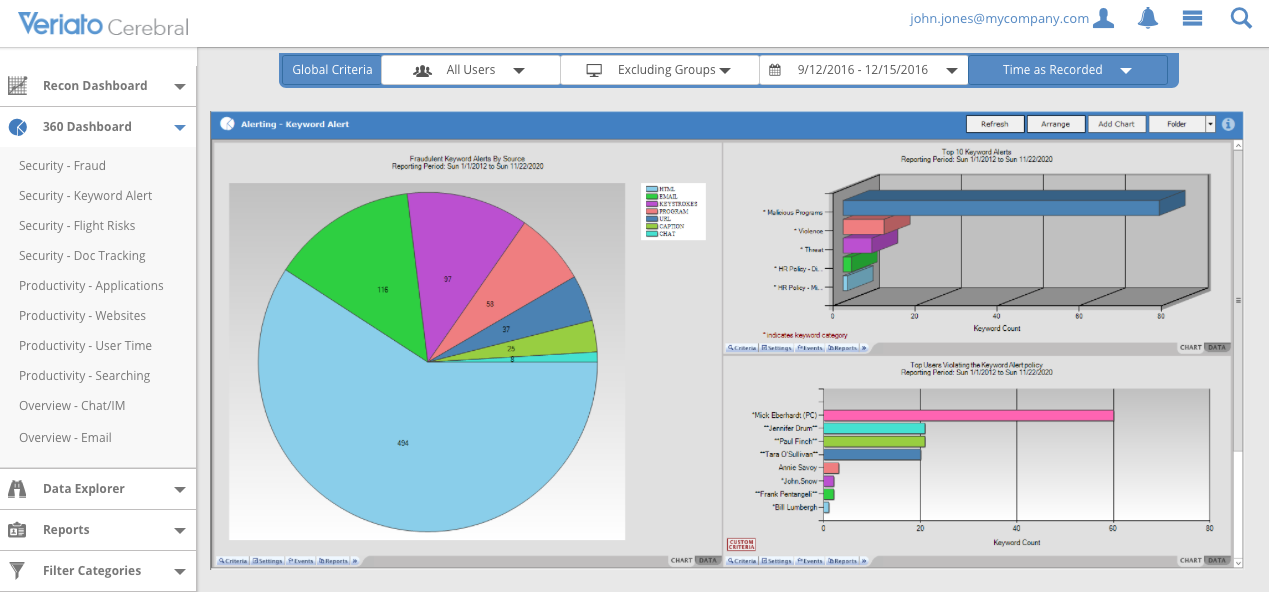
360 Dashboard that includes such tabs as Doc tracking, Keyword Alert, User Time, Email, Fraud.
The distinguishing aspect of the software is its interface that consists of a dual mechanism, which enhances the monitoring – one comes from another. The program is installed on the user’s computer to track every single action that occurs on it, serving as the first level of protection.
It records activities in apps, including messaging ones, and websites, logs emails, printed documents, and files dropped to the USB drives.
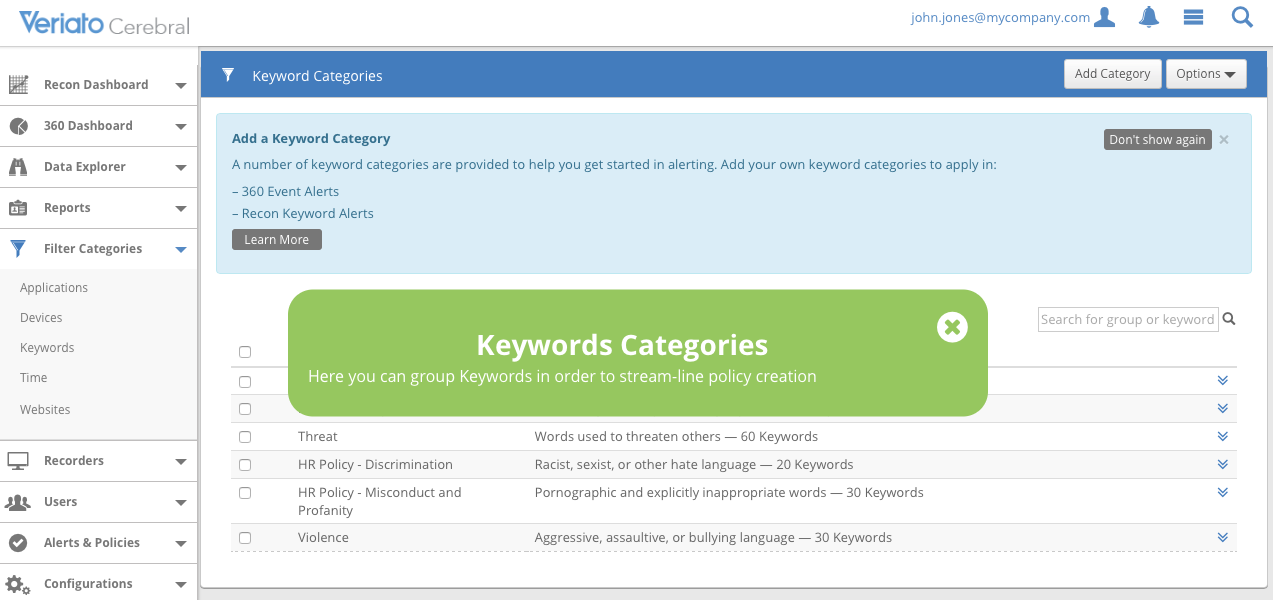
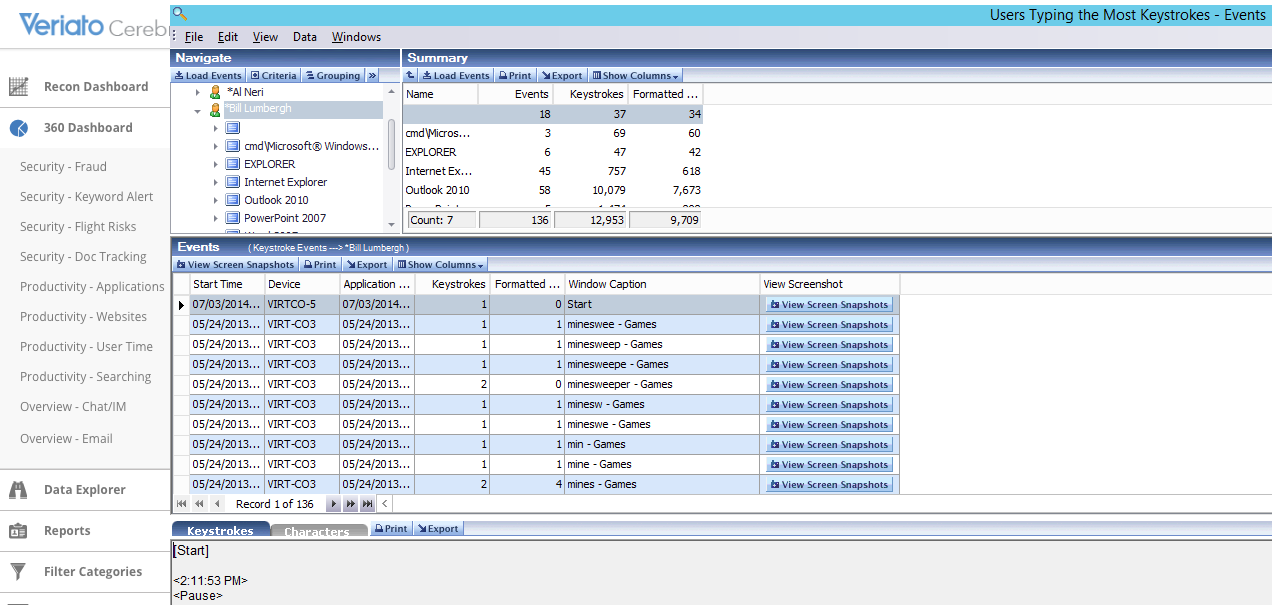
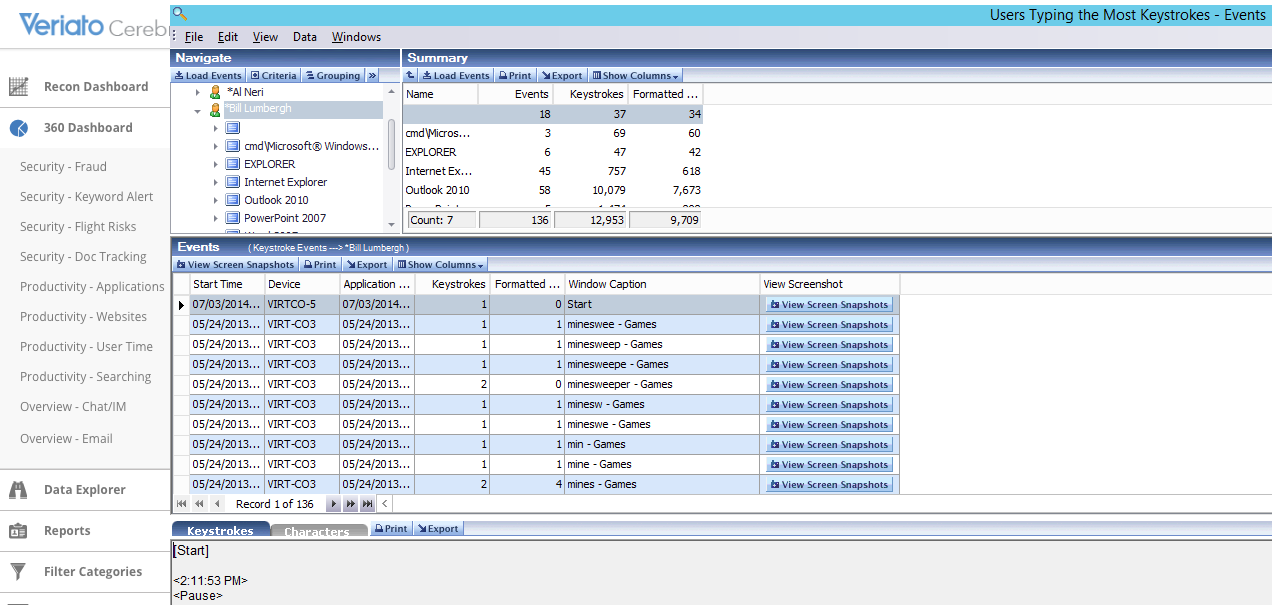
Veriato also contains a keylogging capability that guarantees that any keyword typed by employees is secured and drilled down.
After the information has been captured, it’ll be analyzed.
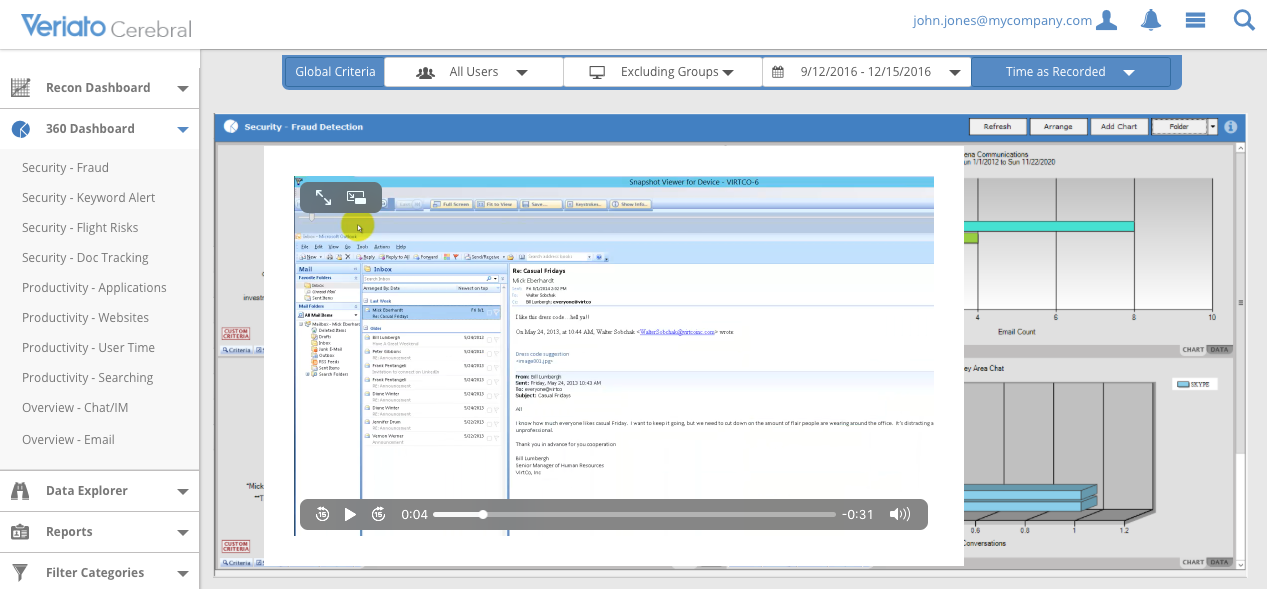
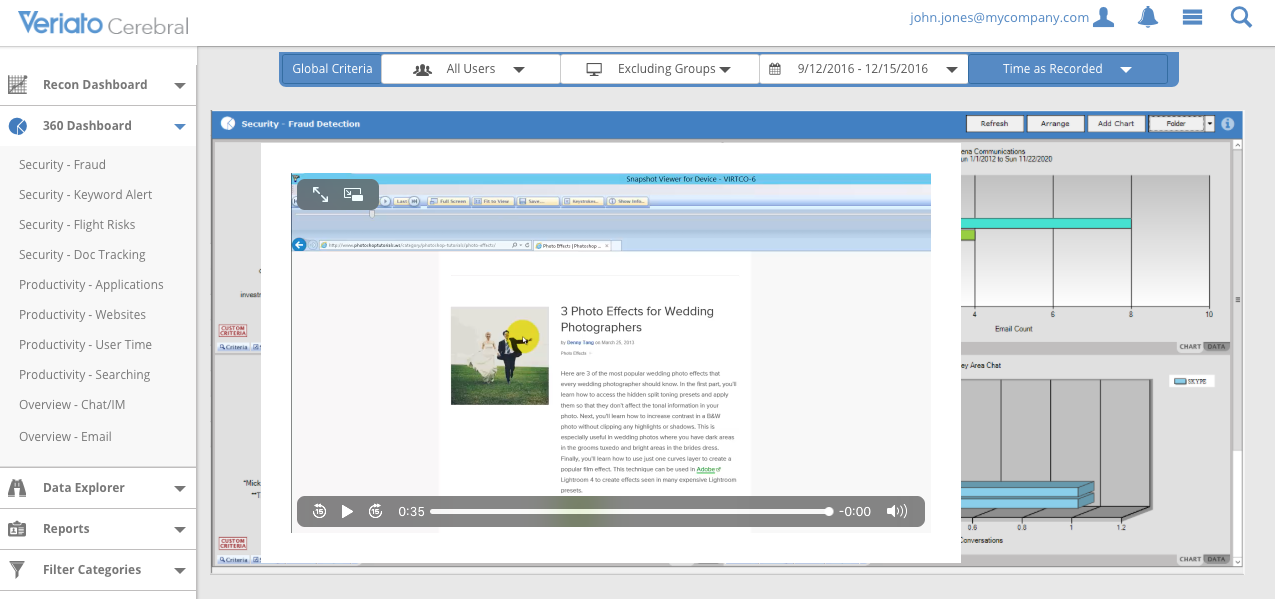
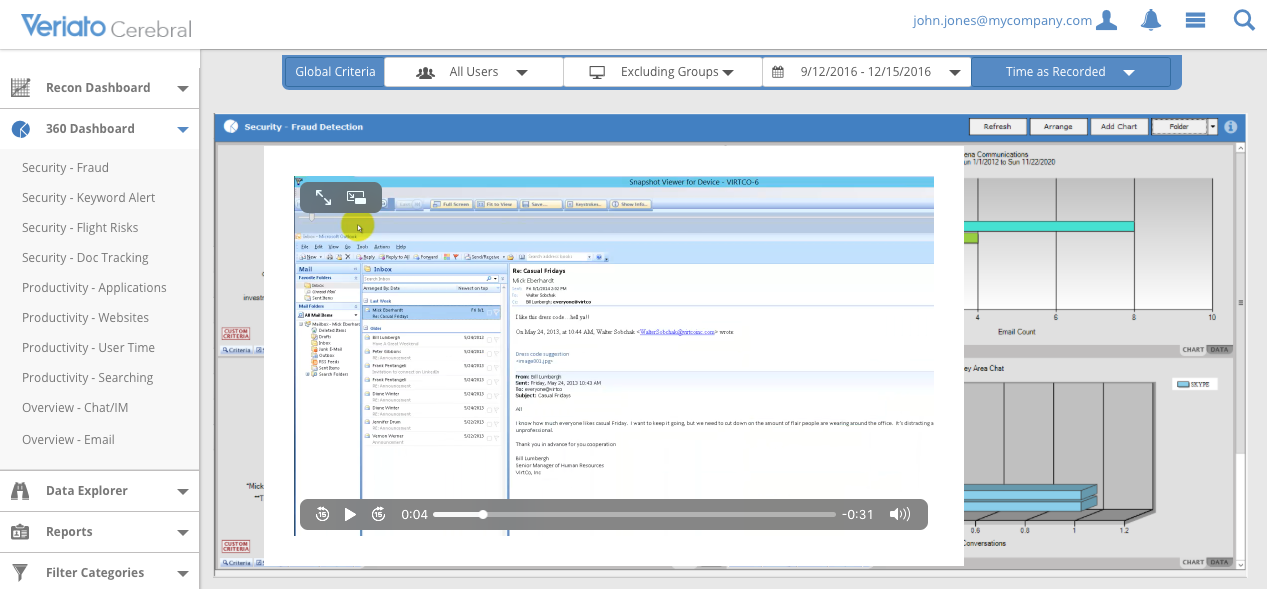
This software allows you to fast-forward the video record of your staff activities during the day, and look through all the important events.
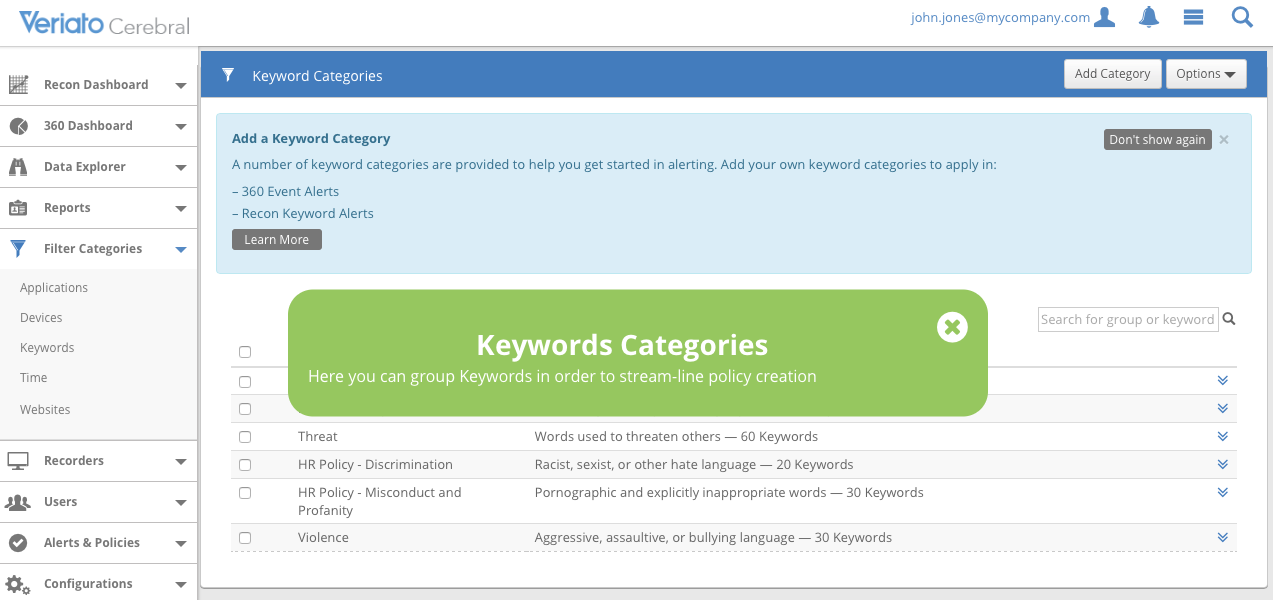
There’s a productivity tracking feature, the software generates alerts triggered by specific keywords in workers’ conversations or when transferring sensitive files.
The degree of control may be set up for specific users or groups of users, it literally provides an investigation level deployment for picking up every piece of information possible. They're less invasive procedures that could be applied for the rest of the staff.
Data is stored on the cloud storage or a local server, for further examination by the supervisors.
Artificial Intelligence is critical for pinpointing potential threats
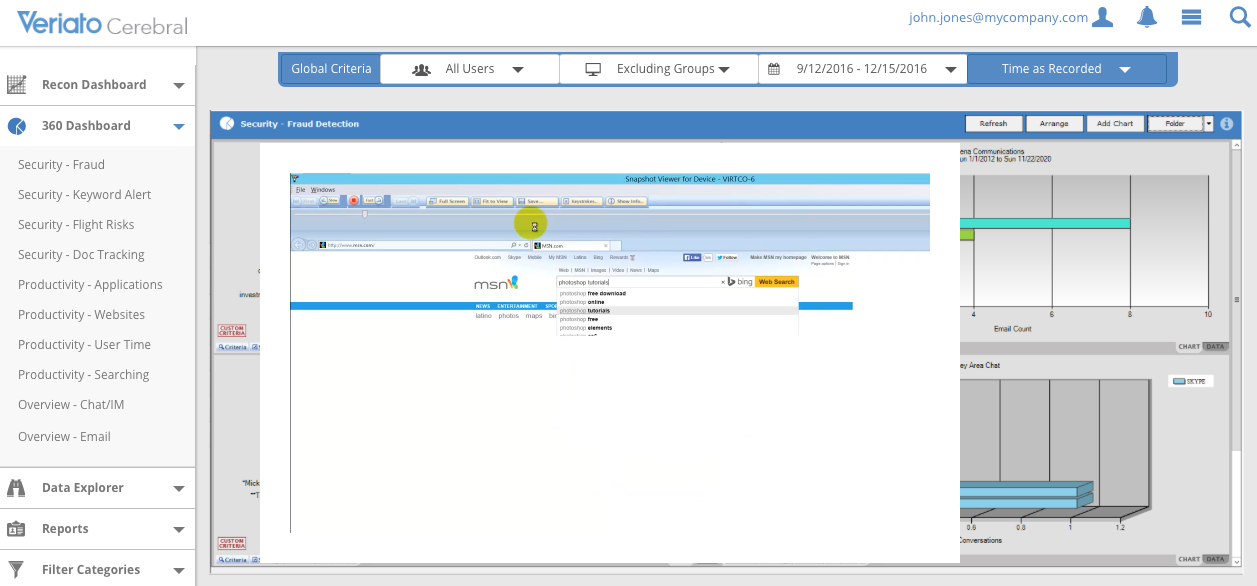
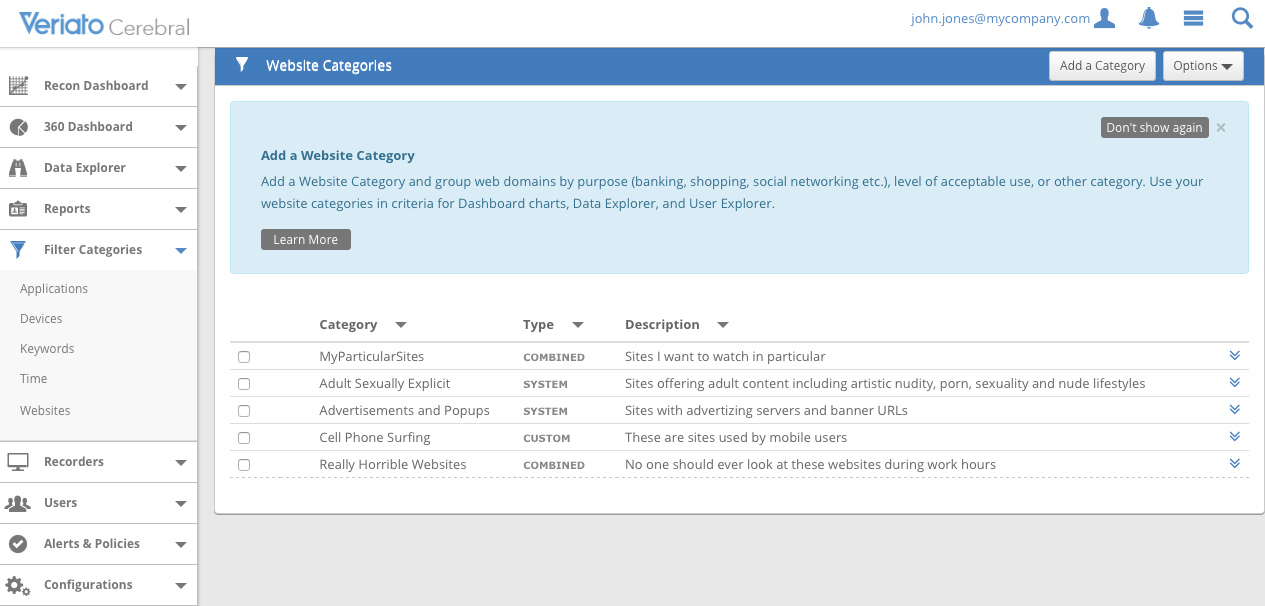
- Web activity of users: This feature keeps a close watch on how employees are using the internet, which websites they visit, browsers they use, and the keyword queries they type. Web activity feature allows you to figure out how long employees stay on webpages.
- Email monitoring: The system monitors email activity in mail services like Gmail. Veriato keeps track of employee email chats, and the exact time those conversations are happening. This feature of Veriato shows admins the email platform, and the text of the particular email. In a few clicks, managers will find keywords or red flags.
- Apps: The system saves the info on the most used employees’ software, in addition to the monitoring of the activity on websites. As an example, the manager will know when employees are playing video games during their working hours.
- File sharing: Information about any uploads/downloads is stored as well and becomes available to the manager. This is useful both in terms of cybersecurity and sensitive document protection. The feature also keeps tabs on things such as BYOD (bring your own device), preventing the storing of sensitive information on the user’s USB drive, for instance.
- Documents: Managers can see all the documents that users create, edit or open. That feature allows admins to find out whether employees might be doing something outside of their tasks.
- Real-time chats: It monitors live chats across popular social media task manager platforms. Among other things, this tool identifies the user and device in question, the participants of the dialogue, the date and time it happened, and the content as well.
- Keystroke logging: Each and every keystroke users make in their apps/browsers are being recorded, so managers could view what users have typed.
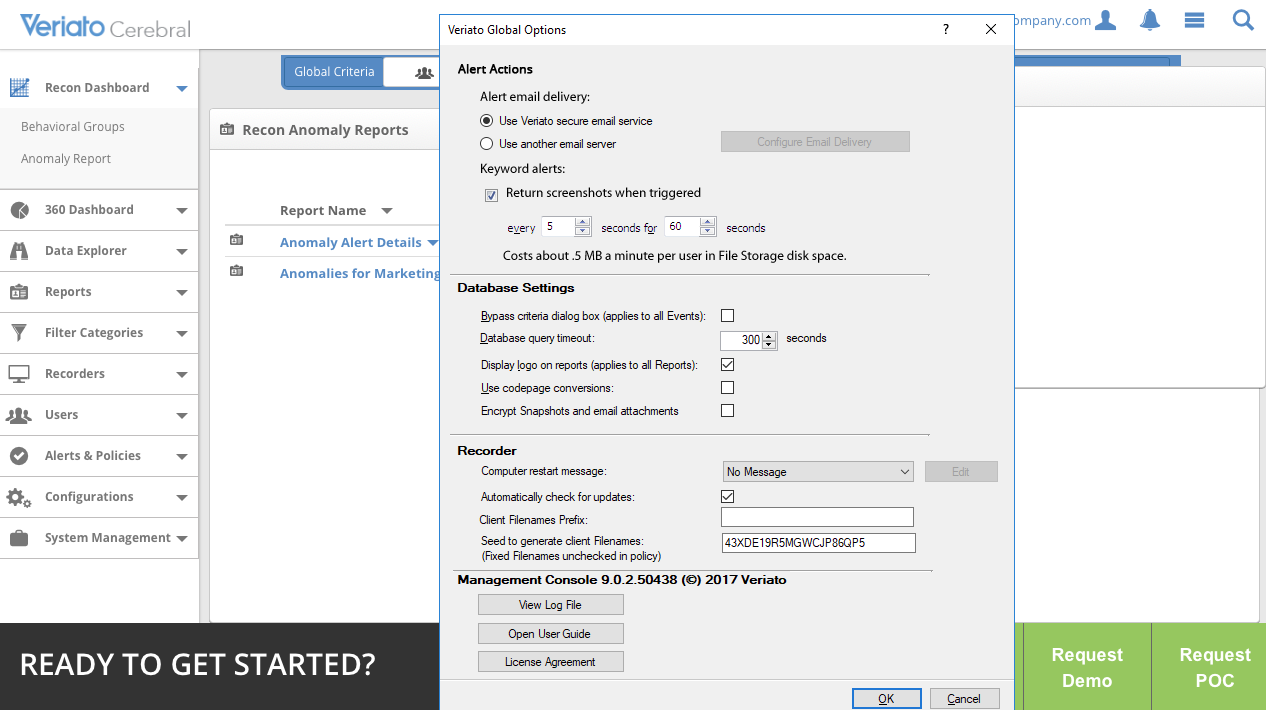
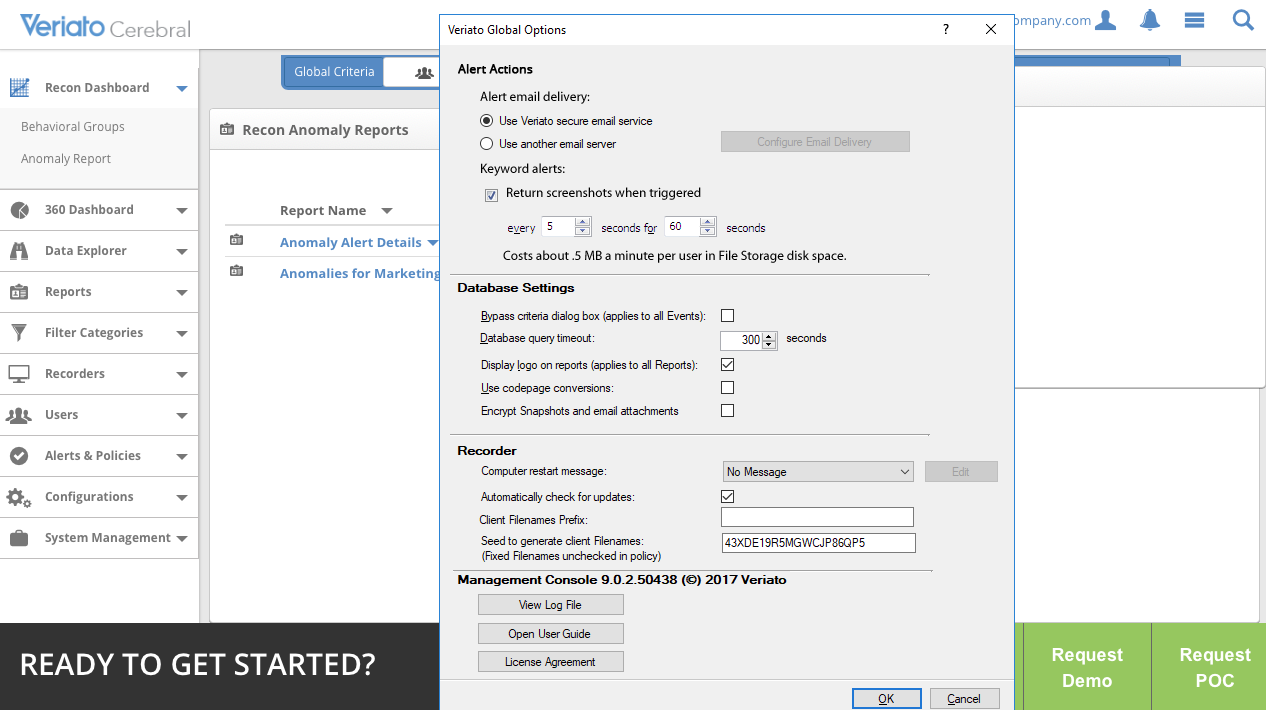
- Real-time notifications: Managers can configure settings for each tool to alert themselves in case of any unusual behavior or breaking the company policy or rules. Notifications that managers receive in real-time, allowing them to identify the time and place the violation has occurred, and then admins can make a quick response.
- Screenshotting: Veriato software allows you to take screenshots and use them as visual proof of users' behavior.
- Video archives: Video archive feature is available for managers, it provides the context of any policy violation. Admins can use video recordings as additional evidence when investigating policy violations.
- Activity time: This feature helps to determine how long employees were remaining inactive. The time during which an employee’s computer remained sluggish is logged. Admins may check it out later.
- Search: The monitoring software stores much data, and it's important to make the search function as intuitive as possible. Managers can set specific triggers to display any piece of data captured by the system, be it events or specific actions of a user on any date.
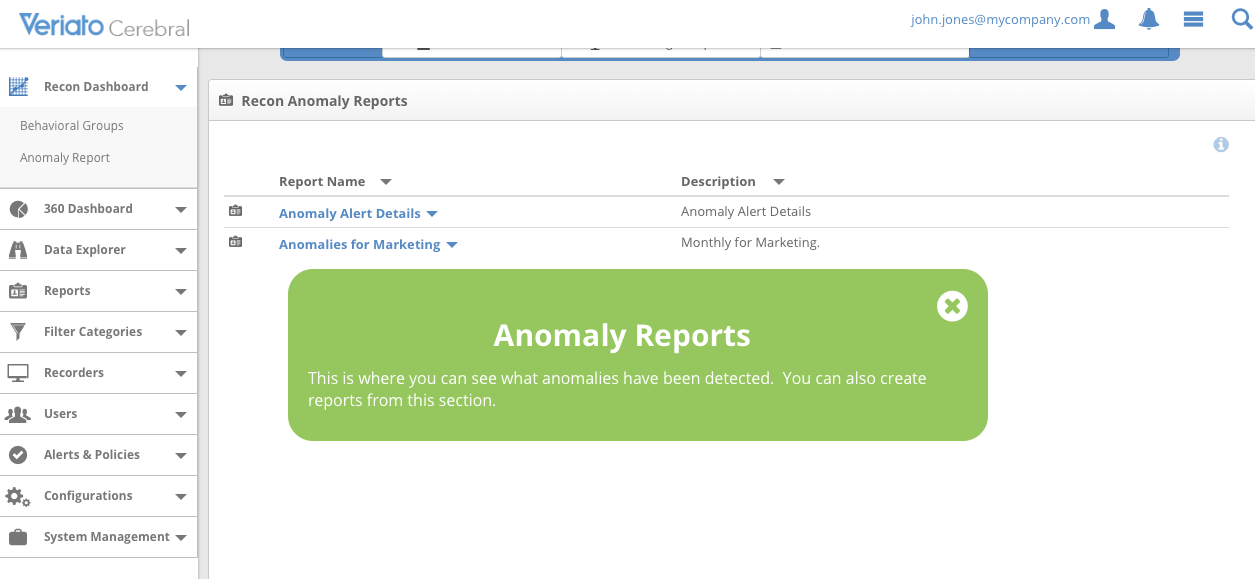
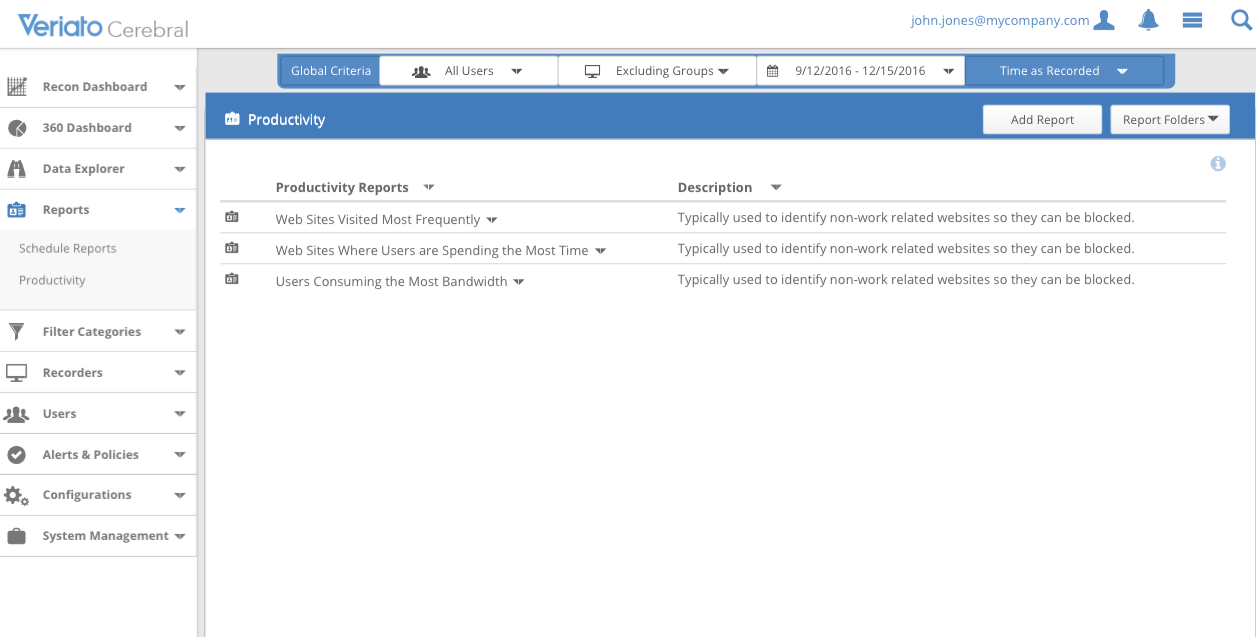
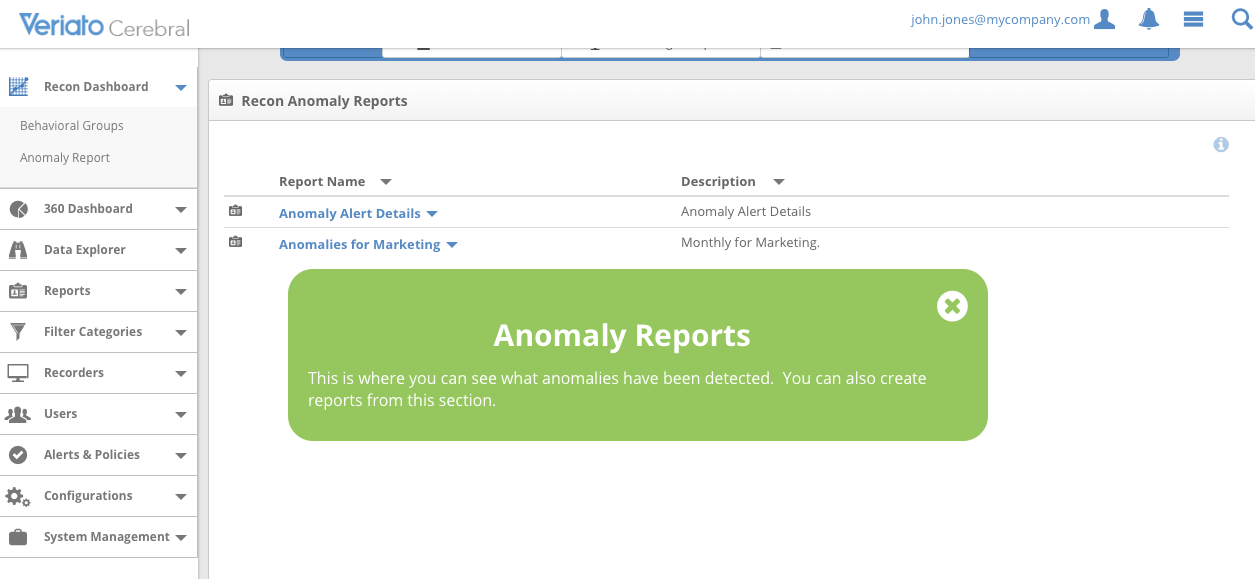
- Reports: The report feature brings up data on a daily, weekly or monthly basis during a certain time. The reports show an employee activity in any applications or websites, with the time of activity and keywords they searched for. You can analyze logged activity in reports. For instance, admin can view social media usage by hour, per employee, or during a week to find out who uses their Facebook or Twitter more than others.
The report showing web activity
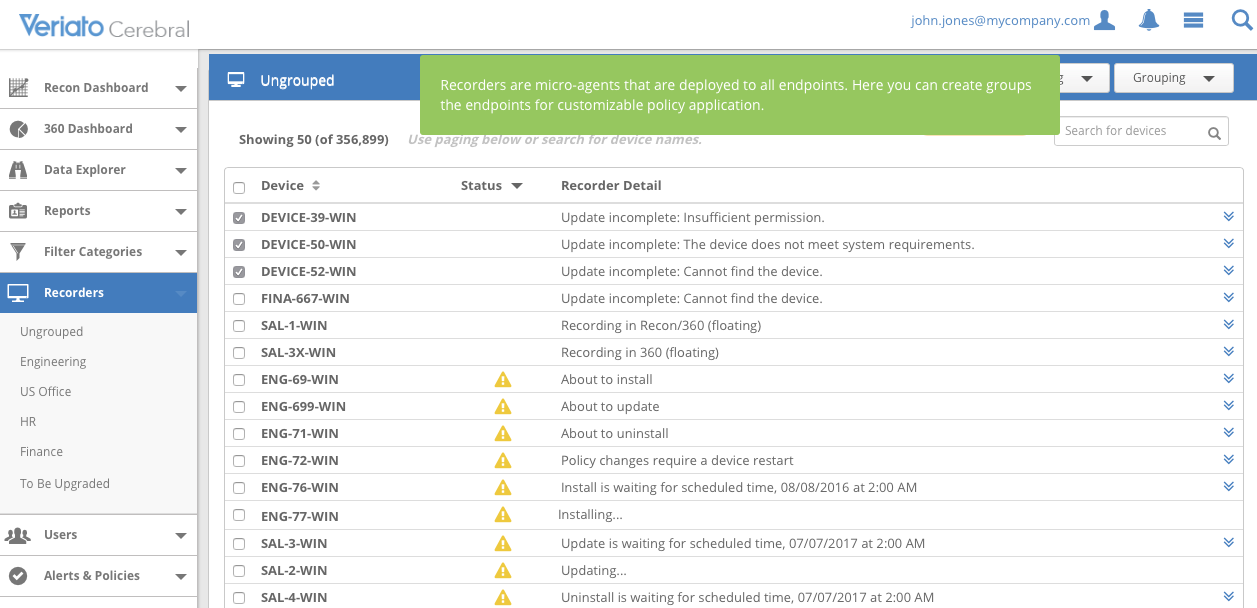
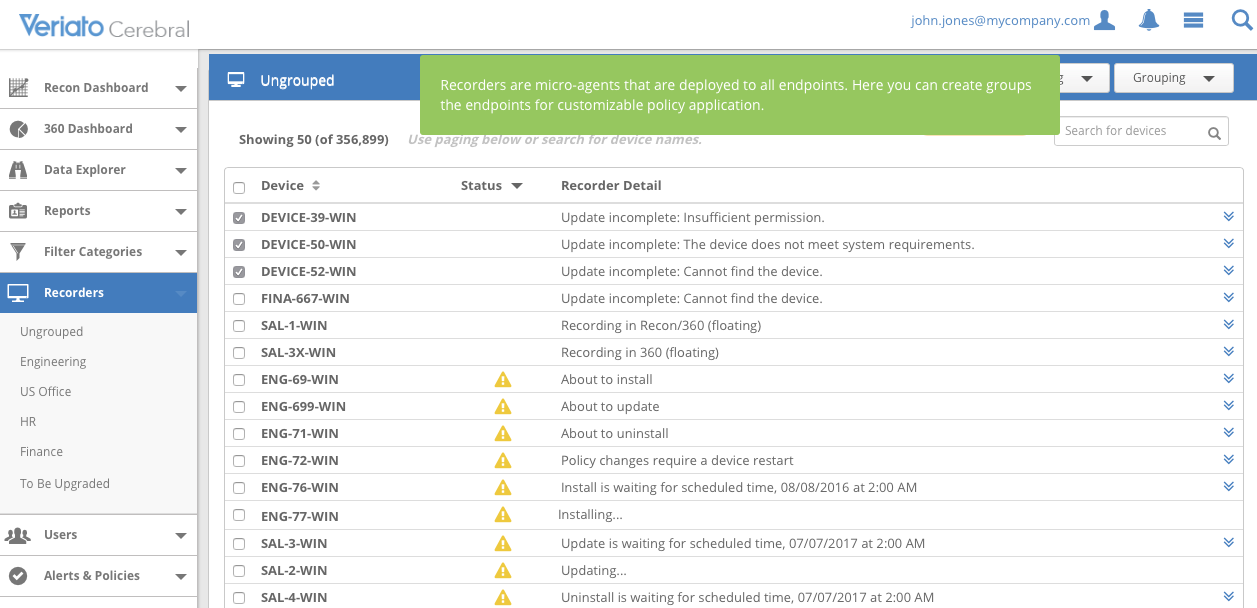
Recorders are micro-agents that are deployed to all endpoints.
The program is set up on Windows, Mac or a smartphone powered by Android.
There’s no iOS or Chromebook version – and that’s the major drawback of this product.
The built-in tool called Insider Threat Detection uses AI code to collect the information and analyze unusual employee’s actions.
Such advanced monitoring technologies might be illegal in some regions. Most of the laws guarantee employees privacy outside of working hours and offices, even when employees might be using company-owned devices.
It must be said that for the correct work of this software every component, like the server, has to be up to date.
Ease of Use
The new version of Veriato Cerebral inherited the interface of its previous iteration, Veriato 360.
The navigation is pretty easy, even newcomers will figure it out. But since it's a comprehensive software, there needs to be a learning curve to master.
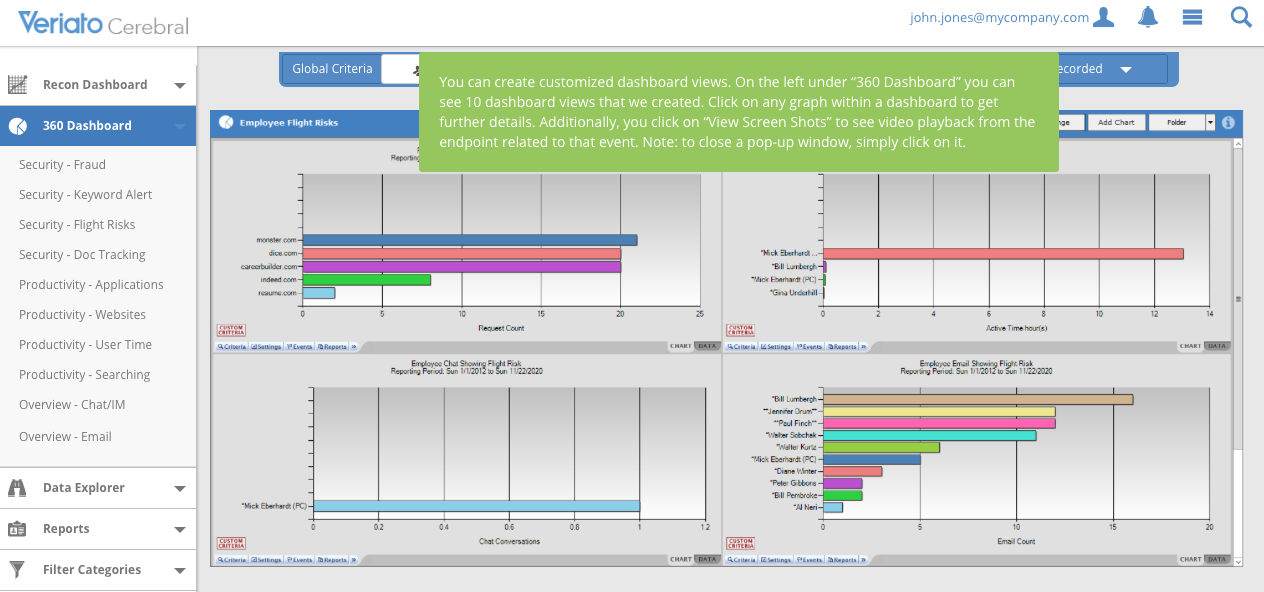
On the first screen, users will see the Cerebral Dashboard, it contains several displays where you can start to monitor productivity, grade the security or check reviews of a particular type of activity. In a way, you can choose the dashboard called Productivity – Websites to check website access by users and by the most frequently banned content.
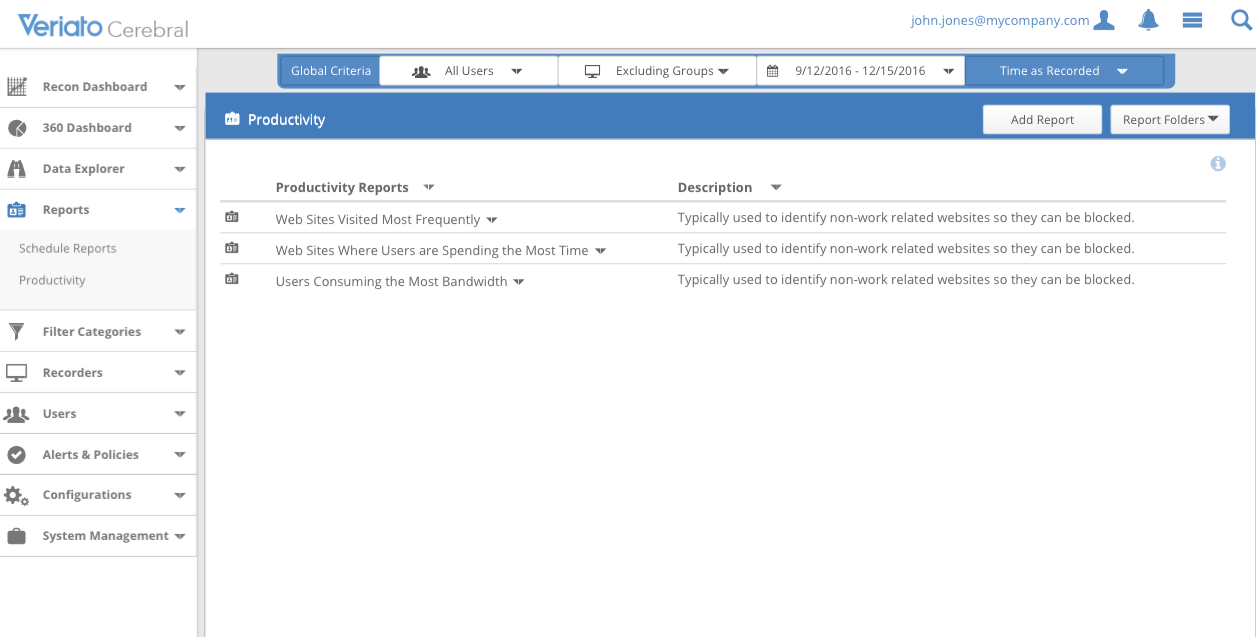
The report on productivity
A similar dashboarding structure applies to apps, user time, searches, fraud alerts, keyword alerts, documents, chats, IM, and email.
There are few dropdown menus on the left of the screen from where you can access the other tools. It could take some time to fully understand Cerebral interface, but while practicing, you’ll have a great deal of control over the system setting your rules, policies, and alerts, as well as monitoring employee behavior for violations or security risks.
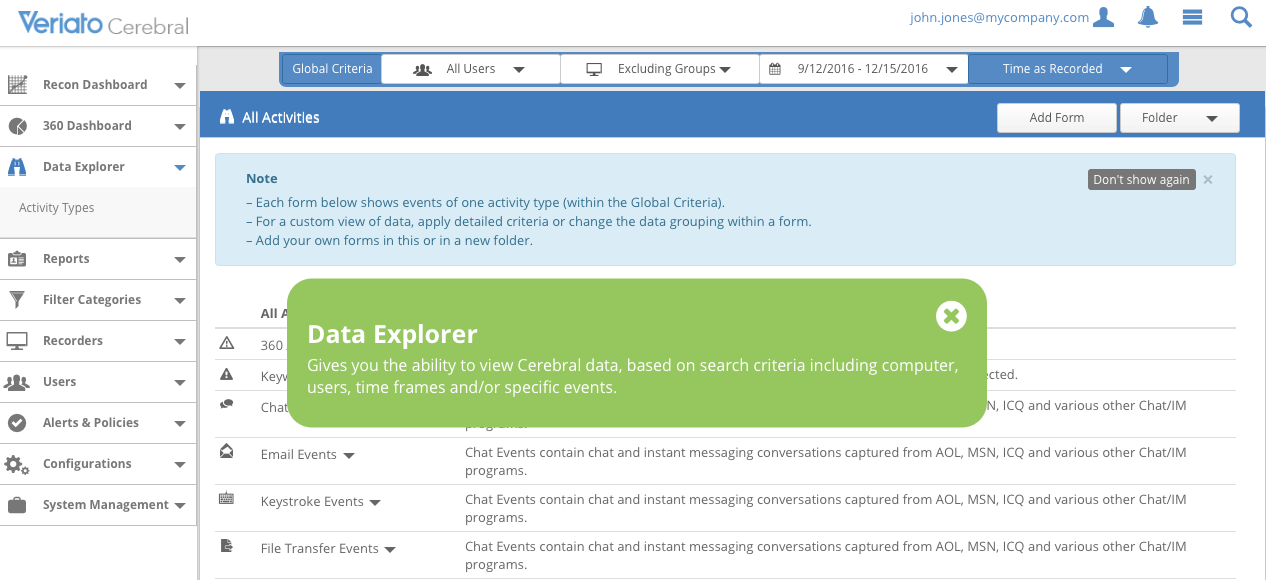
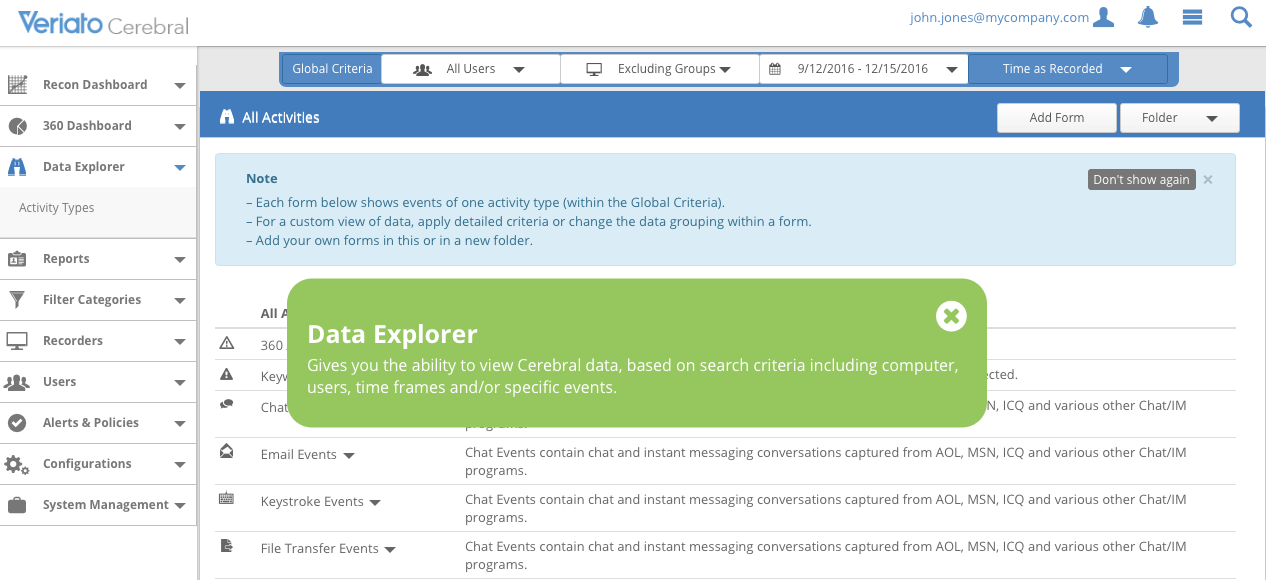
The data explorer based on search criteria: computer, users, time frames.
The data explorer feature allows managers to dive into the data on the dashboard. Using this tool they can track particular activities, users/groups of users, with the search mechanism by date, time, device, specific incidents, etc. That's a great tool to contextualize data because the system captures so much of it. The explorer feature makes them digestible.
Security
That’s a web-based solution, unfortunately, without SSL.
The perpetrators using this vulnerability – via a hacked computer – might get the access and admin passwords, and then get their hand on everything that is on the computers with the Veriato agents installed.
The should be two-factor authentication used in Veriato for admin login, given the importance of the data.
Veriato website contains lots of statistics and other data for people looking for a monitoring solution. For instance, on average employees work less than 3 hours a day. At least this is what their website says.
That specifies neither the tasks those ‘typical workers’ could’ve been doing nor how intensive they were working during their productive hours. But anyway, what is clear is that the employees might be more productive when they are monitored.
The bottom line
The technical side of this product is quite remarkable. Veriato captures all the tiny actions of the employees in fine detail and provides valuable insights.
But, the major weak point of this product is that they haven’t released versions for several popular platforms like Chromebooks or iOS-devices) by now.